Articles
Vergroot je diversiteits bewustzijn en vaardigheden als IT-professional
Diversiteit en inclusie zijn belangrijke thema's voor elke organisatie, maar zeker ook voor de IT-sector. Die te maken heeft met een tekort aan gekwalificeerd personeel, een snelle technologische ontwikkeling en daarbij een groeiende...
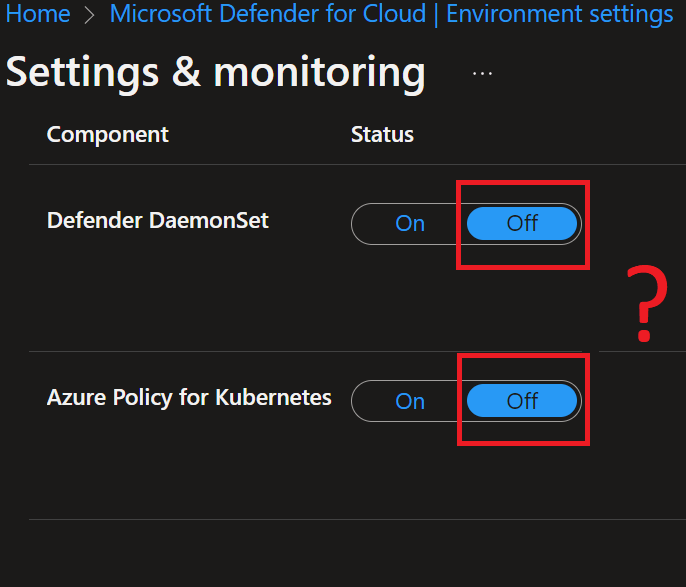
Microsoft Defender for Containers UX unreliability while using policy initiatives for auto-provisioning
Microsoft Defender for containers is a great product to easily add security to your AKS clusters and Azure Container Registries (ACR), both within your Azure infrastructure and for on-premises Kubernetes deployments and using Amazon EKS. The...
Automatically enable Microsoft Defender plans using Azure Policy
I regularly come across Azure environments where the Microsoft Defender plans are not enabled, which is desired. In many cases, the cause can be found in manually managing the environment settings (former 'Pricing Settings'), where all plans must...
Unforeseen Azure Defender for IoT costs, pricing explained
Recently I was confronted with the fact that a subscription with a spending limit was suddenly turned off by exceeding the budget. Because I did not know what caused this, I immediately delved into the cost analysis. Where I found the following:...
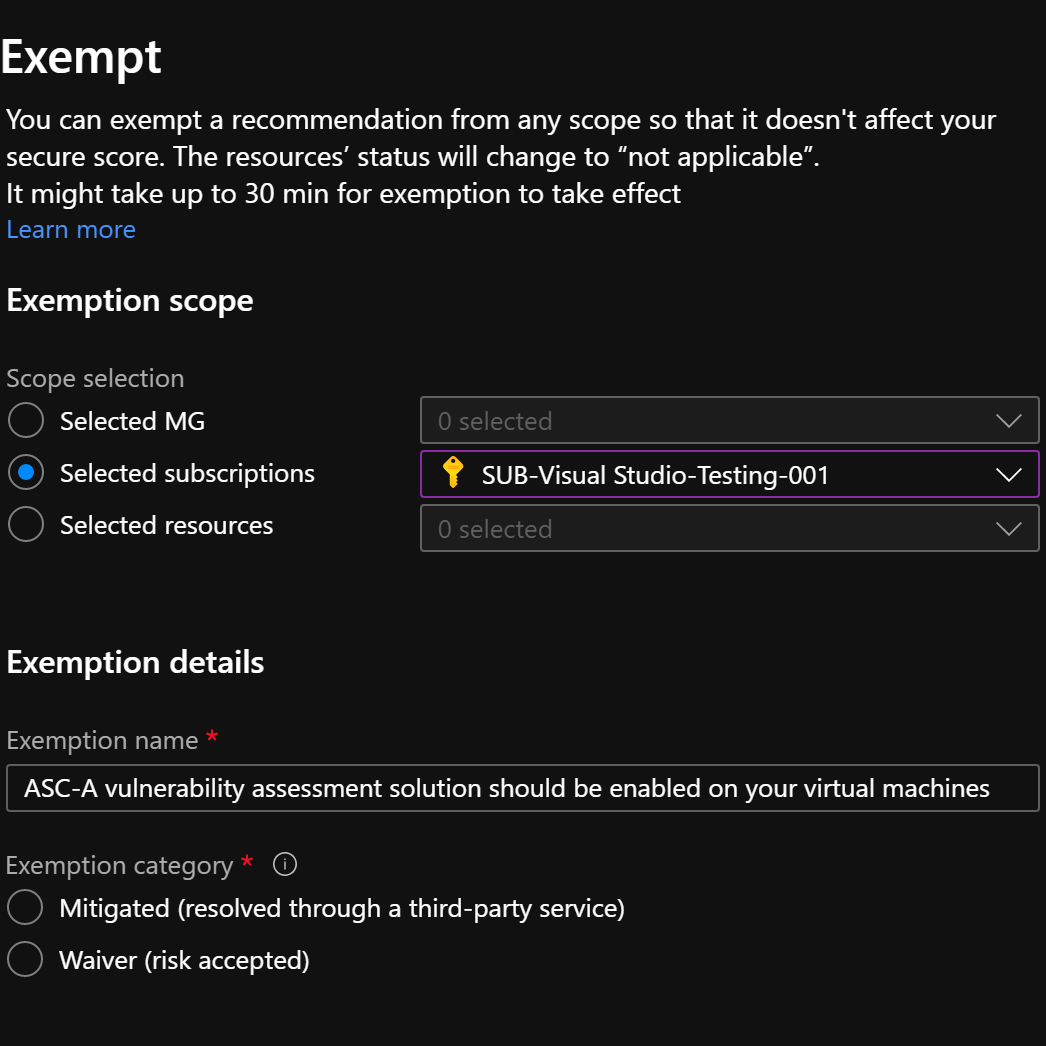
Exempt Azure Security Center recommendations from your secure score on subscription and management group level
Some time ago I wrote about the possibility to exclude a specific resource from an Azure Security Center (ASC) security recommendation (Create an exemption rule to exclude a resource from a security recommendation). With which you can ensure that...
Get insight into your Azure RBAC role assignments
Recently several attacks have been in the news. As a result of this, I received various questions from people with regards to role assignments in their Azure environment: Who exactly has which rights within my Azure environment?At which level are...
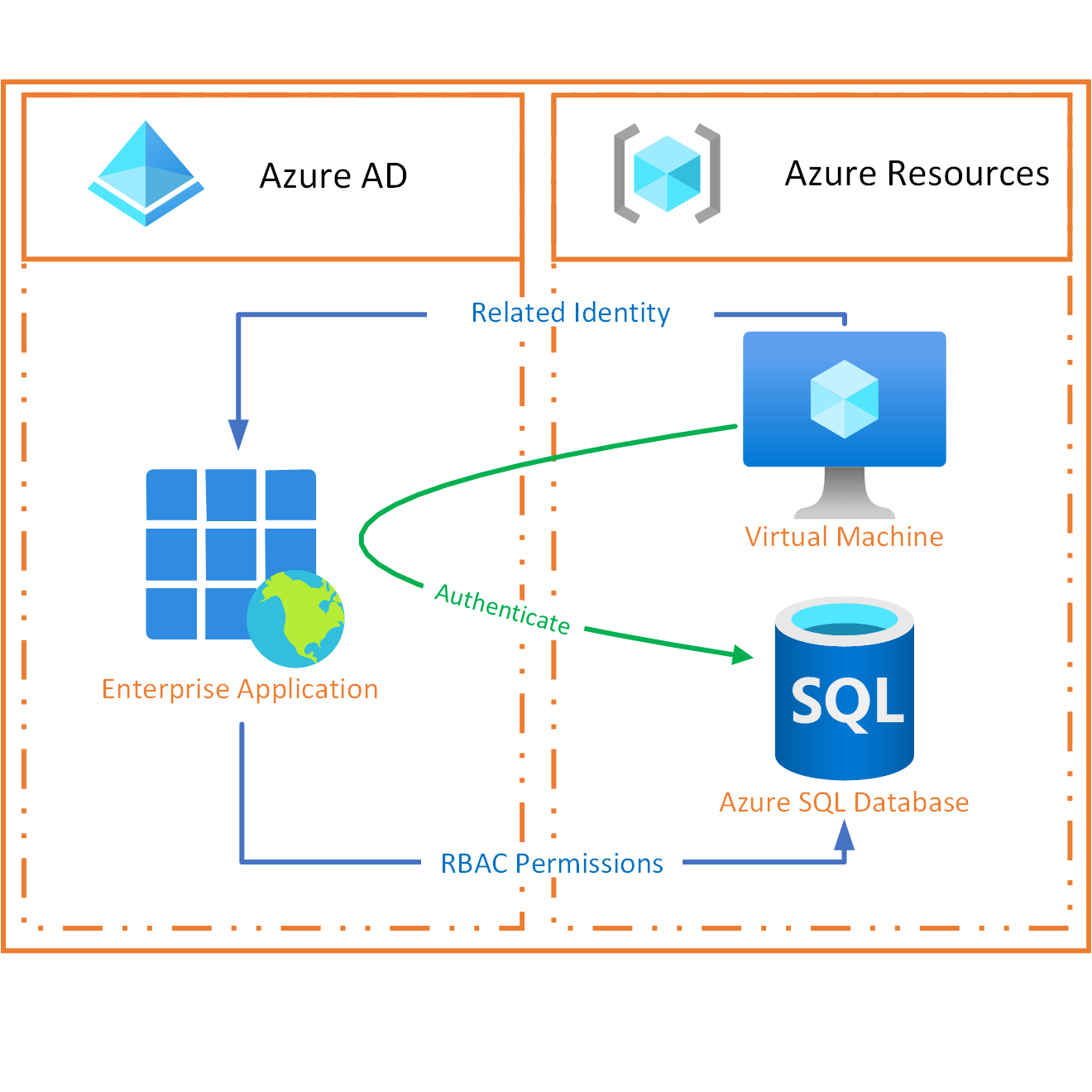
How Azure Managed Identity works explained. A special type of Enterprise Application.
"A special type of Enterprise Application" you may ask. Aren't we talking about Azure Managed Identities here? You are absolutely right! And yet, we cannot avoid talking about Enterprise Applications. I will explain below how this works. If you are...
Default AzureAD Enterprise Applications explained, where do they come from?
Last week I posted an article (The difference between AzureAD App Registrations and Enterprise Applications explained) to which I received many responses. For many people, the difference between App Registrations and Enterprise Applications has...
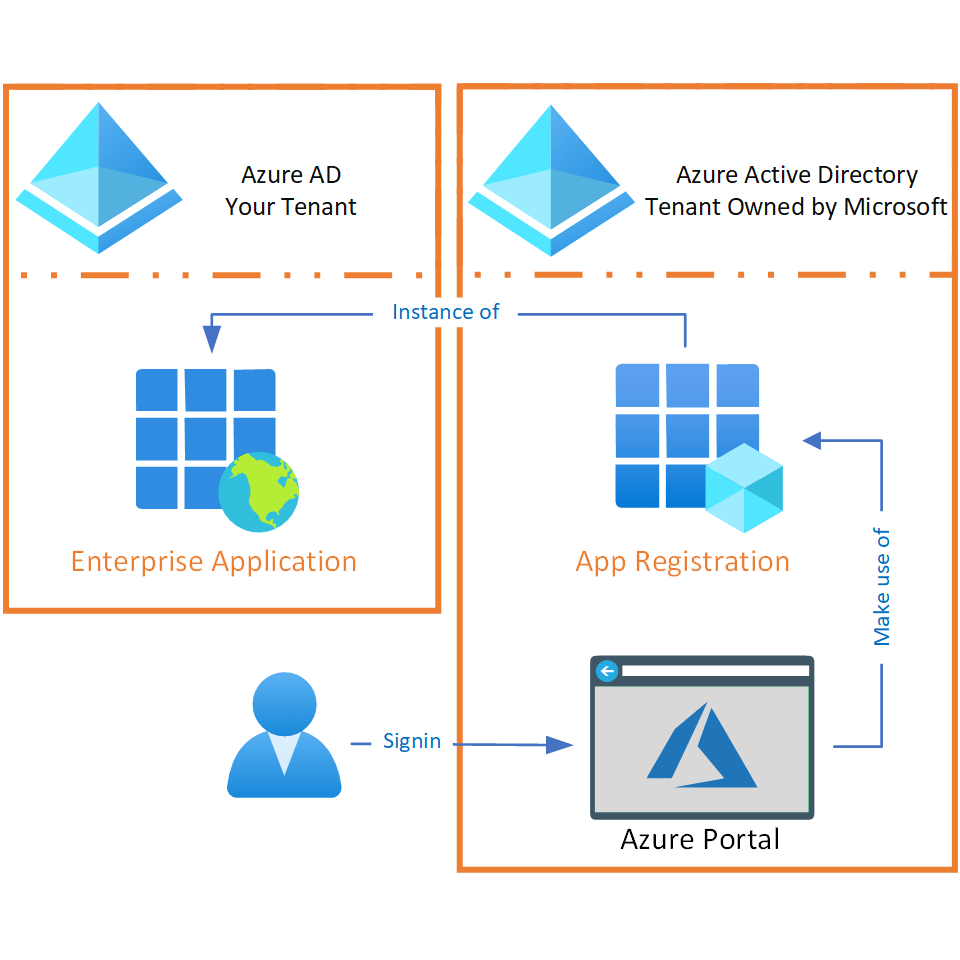
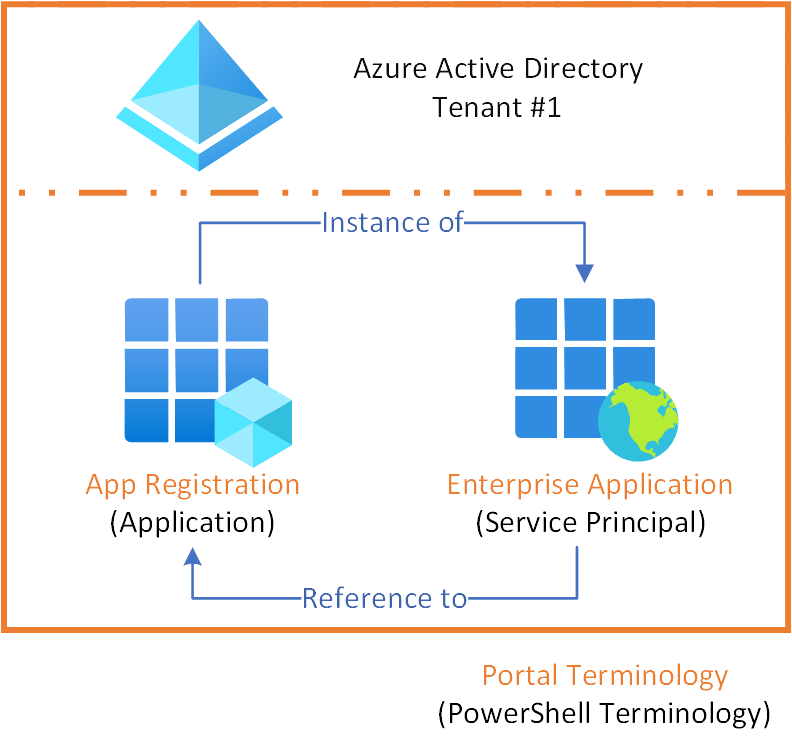
The difference between AzureAD App Registrations and Enterprise Applications explained
The lack of clarity regarding app registrations and enterprise applications is regularly discussed. Both terms are used interchangeably by people and to make it even more unclear, different terminology is used within the Azure portal and for...
Monitor resource management operations and run advanced security analytics to improve resiliency against attacks with the new cloud-native threat protection capabilities of Azure Defender for Resource Manager
Azure Defender provides security alerts and advanced threat protection for all kinds of workloads, like virtual machines, SQL databases, containers and web applications. New plans within Azure Defender are regularly introduced, recently for Key...